Depending on others for knowledge
13 January 2020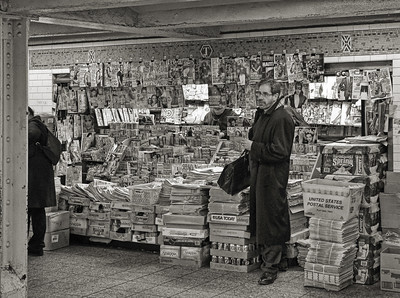
We depend on others. We depend on others when we are sick or when we need help moving into a new house. We also depend on others for knowledge. We learn from books written by other people. Children learn from teachers in school. If we are lost in a city, we depend on others to help point us in the right direction.
Focusing on the last example, if you are lost without access to a (digital) map, finding someone who can help is a good idea. First, you might look around and find someone who doesn’t herself look lost. You might also look for someone who seems available for questioning. The ideal person is someone who is likely to be reliable and receptive to your plight. Depending on how urgent it is for you to quickly make it to your desired destination, you might even ask more than one person. If you do decide to ask a second person, you wouldn’t ask the traveling companion of the first person you asked. You’d want to find someone else, someone who is independent from the first. You do this because you don’t want to depend solely on the knowledge or goodwill of one person when it counts.
Consider another example. Imagine you are diagnosed with a serious medical condition. It is not the kind of condition that is life threatening, but one that requires major lifestyle changes and daily medication. Since the diagnosis is life altering you seek a second opinion. However, not just any second opinion will do. The second opinion should be in some way independent from the first. This might require going to another medical practice down the road. You do this because you don’t want to depend solely on the knowledge or goodwill of one person, or one clinic, when it counts. After all, the whole point of a second opinion is to get a fresh perspective on the medical evidence at hand. Doctors in the same clinic talk, which can muddle the fresh perspective you are seeking.
Network epistemology takes as its starting point that we are all embedded in an inter-connected epistemic community of dependence.[1] It says that in order to evaluate our epistemic lives, we need to see the structure of this dependence and the degree to which our epistemic lives depend on the goodwill—or true beliefs—of a few. The broader and more independent our sources are within our epistemic communities, the less dependent we are on the goodwill of others and the greater opportunity we have for sustained epistemic growth and intellectual autonomy.
For example, in a star network (Fig. 1) information is filtered through a single central source. The center node (the source node) is the only source the outer nodes rely on for information. Each outer node is dependent on the single center node. Epistemic networks that are structured like star networks are associated with a number of problematic and harmful practices. Sexual predators and their targets often form a star network, with the predator at the center and the victims on the points of the star. This keeps the victims from effectively communicating with one another, and coordinating or cooperating against the predator.[2] Star networks are also associated with financial fraud,[3] academic fraud,[4] and terrorist activities.[5] This isn’t surprising when we notice that a star network forms a structure of dependence that can easily lead to epistemic manipulation. If someone has only one source of information on a particular subject, and that source works to limit communication between others that utilize that source, there is no space for intersubjective validation. The more dependent we are on a few people, the more insecure our epistemic network is, and the more vulnerable we are to manipulation.

Fig. 1 Star Network
Network-security is worth aiming for even if it does not increase the likelihood of true beliefs. To see why, consider a non-epistemic case drawn from the history of philosophy. Kant put forward an argument that political rights are necessary for personal freedom and autonomy. Without these rights, the well-being of people is dependent on the goodwill of the strong or the state. In the case where the strong or the leader of a society has goodwill, political rights don’t make a practical difference to those living in the society. However, their well-being is still less secure. If the leader is replaced, or the strong have a change of heart (for the worse), then the weak have no protections. So even if political security does not make a practical difference in the day-to-day lives of people, having those rights secures personal freedom and autonomy currently, and in the case of change. Otherwise, it is just a matter of luck, or happenstance, that each person’s well-being is respected.
We find analogous results in the epistemic case. If you are in an insecure epistemic network, like a star network, but the source you rely on is reliable, trustworthy and accurate, then it might seem as though nothing is epistemically out of place. After all, you have access to true and reliable information. However, there is a strong sense in which your level of epistemic autonomy is diminished, with little opportunity to grow epistemically. In a star network, there is no exchange of differing ideas, and such exchanges can spur independent, critical, and creative thought. Moreover, just as in the political case, if the source has a change of heart, whatever good epistemic position you had is lost, without any clear opportunity to redeem it. You might not even notice something has changed.
[1] Sullivan, E., Sondag, M., Rutter, I., Meulemans, W., Cunningham, S., Speckmann, B., & Alfano, M. (2019). Can Real Social Epistemic Networks Deliver the Wisdom of Crowds?, in Oxford Studies in Experimental Philosophy (Vol. 3). Eds. Lombrozo, T., Knobe, J., & Nichols, S. Oxford University Press.
Sullivan, E. & Alfano, M. (forthcoming). Vectors of Epistemic Insecurity, in Vice Epistemology Theory and Practice. Eds. Ian Kidd, Quassim Cassam, and Heather Battaly, Routledge.
[2] Alfano, M. (2016). The topology of communities of trust. Russian Sociological Review, 15(4): 30-56.
Fire M., Katz G., Elovici Y. (2012) Strangers Intrusion Detection: Detecting Spammers and Fake Profiles in Social Networks Based on Topology Anomalies. Human Journal, vol. 1, no 1, pp. 26–39.
[3] Šubelj L., Furlan U., Bajec M. (2011) An Expert System for Detecting Automobiles Insurance Fraud Using Social Network Analysis. Expert Systems Applications, vol. 38, no 1, pp. 1039–1052.
[4] Callaway E. (2011) Report Finds Massive Fraud at Dutch Universities. Nature, 479, p. 15.
[5] Krebs V. (2002) Mapping Networks of Terrorist Cells. Connections, vol. 24, no 3, pp. 43–52.
Reid E., Qin J., Zhou Y., Lai G., Sageman M., Weimann G., Chen H. (2005) Collecting and Analyzing the Presence of Terrorists on the Web: A Case Study of Jihad Websites. Intelligence and Security Informatics (eds. P. Kantor, G. Muresan, F. Roberts, D. D. Zeng, F. Y. Wang, H. C. Chen, R. C. Merkle), Berlin: Springer, pp. 402–411.
- July 2024
- June 2024
- May 2024
- April 2024
- March 2024
- February 2024
- January 2024
- December 2023
- November 2023
- October 2023
- September 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- March 2023
- February 2023
- January 2023
- December 2022
- November 2022
- October 2022
- September 2022
- August 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
- September 2021
- August 2021
- July 2021
- June 2021
- May 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- August 2020
- July 2020
- June 2020
- May 2020
- April 2020
- March 2020
- February 2020
- January 2020
- December 2019
- November 2019
- October 2019
- September 2019
- August 2019
- July 2019
- June 2019
- May 2019
- April 2019
- March 2019
- February 2019
- January 2019
- December 2018
- November 2018
- October 2018
- September 2018
- August 2018
- July 2018
- June 2018
- May 2018
- April 2018
- March 2018
- February 2018
- January 2018
- December 2017
- November 2017
- October 2017
- September 2017
- August 2017
- July 2017
- June 2017
- May 2017

